Secure your IaaS VMs with Duo Security
Deploying a developer or jump VM in the cloud can be easily done but once you add a public IP address to your VM you are exposed. Attackers consistently scan cloud providers IP ranges to locate machines with exposed management end points. Once detected, attackers will try to brute force and exploit these end points, taking advantage of new machines with weak passwords and/or bad configurations.
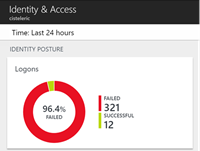
As an example, I deployed a VM and left it running for 24 hours and had 321 failed login attempts.
Using Duo Security, I can add two-factor authentication to all Windows logins via local console or RDP. Duo provides a free version that supports up to 10 users. Check out the plans comparison table to find out which version is right for you: https://duo.com/pricing
The setup of Duo Authentication was extremely easy and was accomplished in 5 easy steps:
- Sign up for a Duo account. https://signup.duosecurity.com/
- Log in to the Duo Admin Panel and navigate to Applications.
-
Click Protect an Application and locate Microsoft RDP in the applications list.
-
Click Protect this Application to get your integration key, secret key, and API hostname.
- Download the Duo Authentication for Windows Logon Installer Package.
If you want to install the package silently from the command line of powershell, you can use the following command: duo-win-login-latest.exe /S /V” /qn IKEY=”xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx” SKEY=”xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx” HOST=”api-XXXXXX.duosecurity.com” AUTOPUSH=”#1” FAILOPEN=”#0” RDPONLY=”#0””
Once the agent is installed on your server, you simply logout and when you re-login you will be prompted by Duo Security to authenticate with your phone.